Scytale named Leader in G2’s 2024 Fall Reports with top spots in Governance, Risk, Compliance & Security Compliance across multiple ...
Everything you need to achieve and maintain compliance without losing business, time, or money in the compliance rabbit hole.
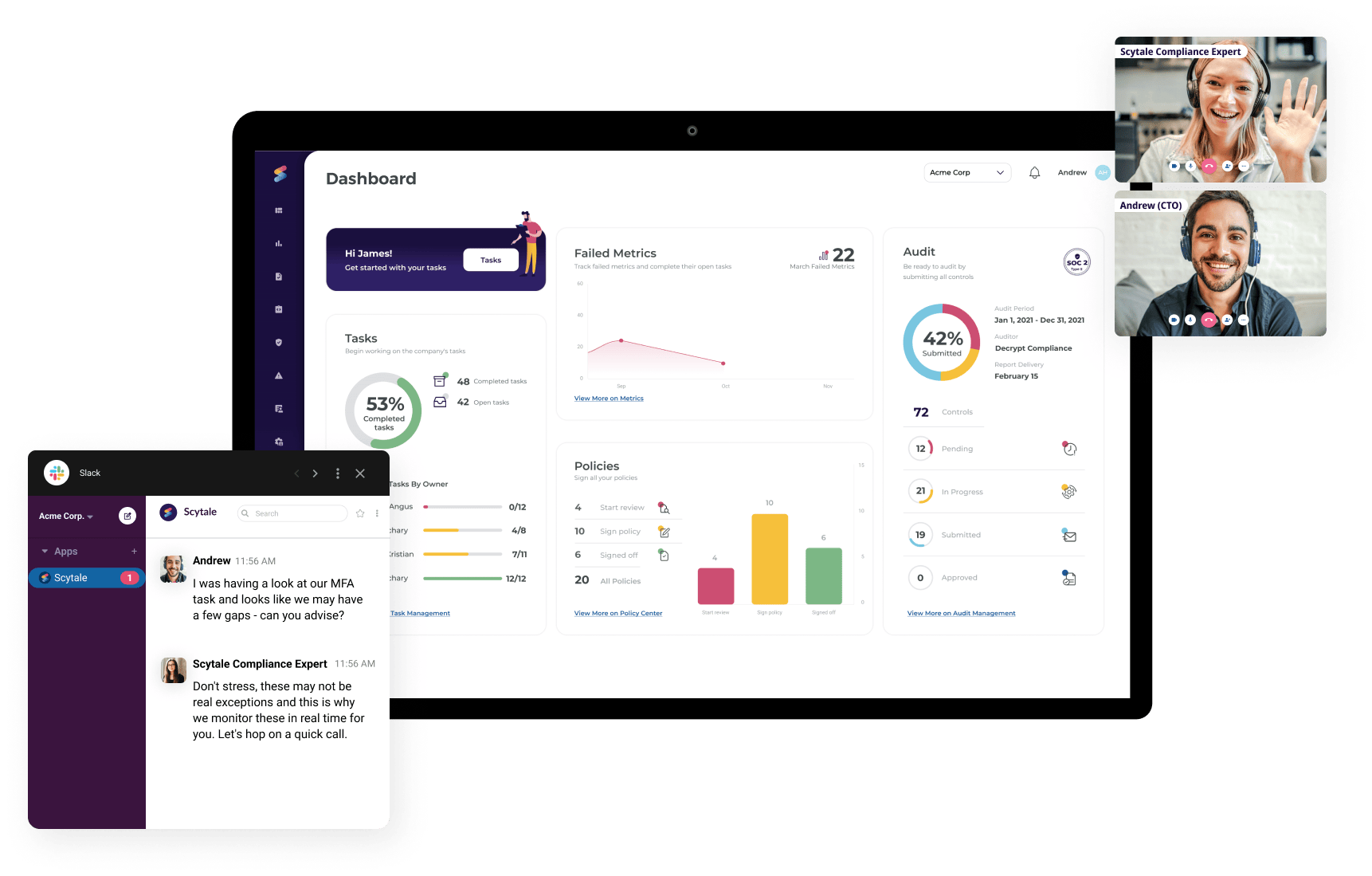
Meet your dedicated compliance expert and define your audit scope
Automated risk assessment and control implementation
Integrate your tech stack and collect evidence automatically
Complete audit (if applicable)
Continuous control monitoring


Security compliance made easy because the alternative really isn’t. Replace the risk of data breaches, losing big deals, and global market restrictions with an easy-to-track automated solution with everything you need in one place.
Let’s face it. Nothing beats a dedicated human expert, leading you through the intricacies of your compliance journey. It’s simple – we’re the compliance experts so you don’t have to be!
As your business or software scales, so does your exposure to sensitive data. Heads up: you’re not too small to slip under the radar. Instead of running after evidence or chasing compliance updates – protect your business and customers’ data in one fell swoop. At Scytale, we help you build and maintain a security posture to defend your business, headache-free.
Monitor your controls 24/7 and be alerted immediately when there is a non-compliance
Make access reviews a walk in the park with automation

leverage controls mapped from other security standards and regulations
Easily monitor and manage all risks associated with your vendors
Easily monitor and manage all risks associated with your vendors
Integrate your tech stack seamlessly and unlock automatic evidence collection
Learn how the right compliance framework can help your business expand into new markets, secure bigger deals, and leverage a competitive advantage. Browse through more than a dozen of our security and privacy frameworks

Automate your audit-readiness process and boost customer trust by complying with the AICPA's Trust Services Criteria.

Meet the international gold standard and build your information security management system (ISMS) by streamlining compliance.

Ensure you're storing, managing and transferring protected health information (PHI) securely and automate your HIPAA compliance.

Comply with the European regulation on privacy and data protection by streamlining your compliance journey.
Scytale named Leader in G2’s 2024 Fall Reports with top spots in Governance, Risk, Compliance & Security Compliance across multiple ...
This guide explores how penetration testing enhances security and ensures compliance for SaaS companies with SOC 2 and PCI DSS.
Discover how NIST password guidelines evolved to prioritize longer, user-friendly passwords, reducing resets and boosting security for 2024.
Explore PCI DSS audit costs, key factors that influence pricing, and practical tips for managing and optimizing your compliance expenses.
Explore the differences between CMMC and NIST to enhance your cybersecurity posture and secure government contracts.
Learn how to navigate the DORA compliance checklist and meet DORA cybersecurity regulation requirements with our step-by-step guide.
In this tech talk with Mischa, Scytale's CSM, explore balancing AI innovation with responsibility, focusing on bias and transparency.
Discover the key differences between SOC 2 and NIST to choose the right cybersecurity framework for your organization.
In this article, we’re focusing on HIPAA compliance and how your organization can stay ahead of the compliance curve.
Discover why ISO 27001 certification is crucial. Enhance data security, compliance, and credibility while unlocking global opportunities.
As you prepare your business strategy for the second half of 2024, regulatory compliance automation should be a top priority.
Hear Robyn Ferreira as she breaks down how Scytale’s Continuous Compliance feature monitors your systems 24/7 to keep you compliant.
Discover the key differences between SOC 2 and SAS 70, and learn why SOC 2 is the modern standard for ensuring data security and compliance.
Explore essential risk assessment methodologies to safeguard your organization and find the best fit for your needs.
HITRUST vs. ISO 27001: Compare the two frameworks and choose the best fit for your organization's security needs.



