Scytale streamlines the entire SOC 2 process – automating everything from audit prep to continuous monitoring – so your team can focus on growth, while we keep you compliant around the clock.
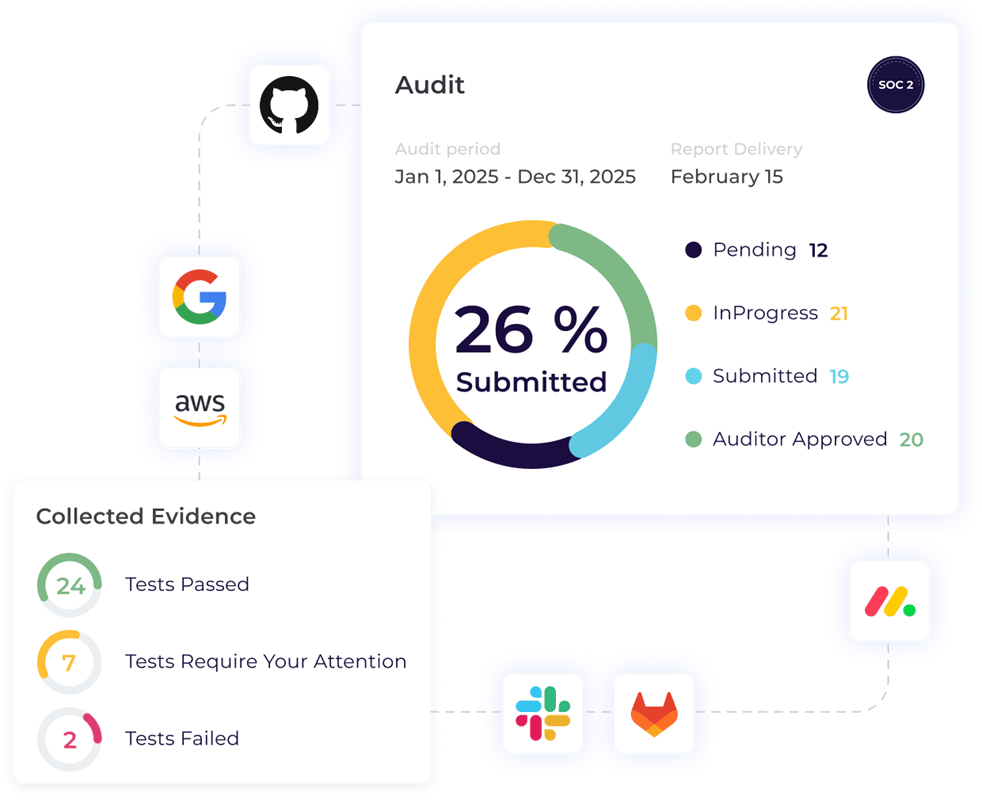
Scytale syncs with all your favorite tools to automatically collect and verify the evidence you need in a format that auditors recognize and trust, saving you from tedious manual work.

Compliance never sleeps and Scytale ensures ongoing SOC 2 compliance beyond your audit by monitoring the effectiveness of your controls 24/7, so you’ll never have to guess where you stand with SOC 2.
Scytale’s dedicated GRC experts are with you every step of the way – guiding you through every audit requirement so you never have to face SOC 2 compliance alone.

Leverage Scy, our very own AI GRC-agent. From risk management to evidence and policy reviews, you can now automate complex compliance tasks, reducing your daily cognitive workload by a mile.
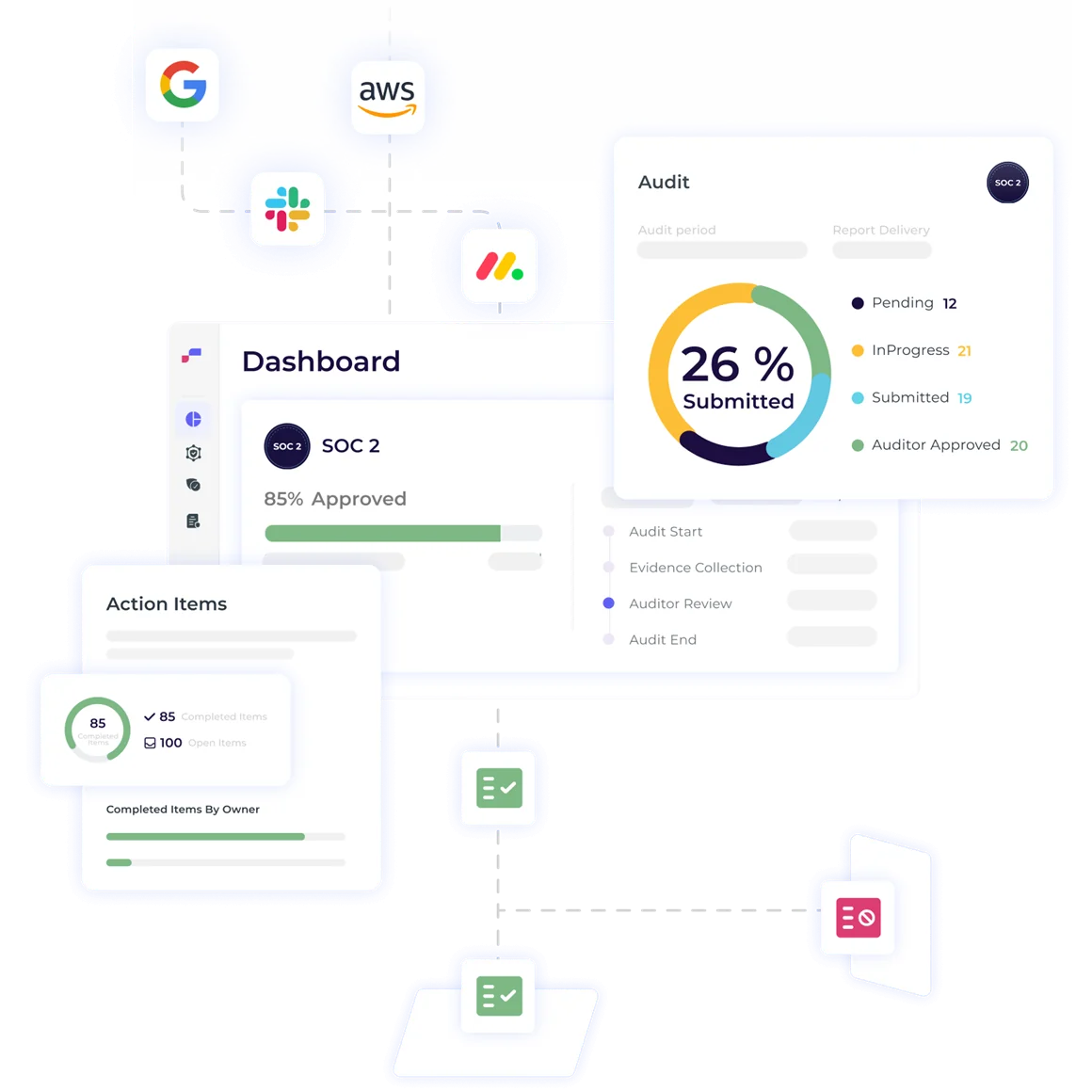
Work with a dedicated audit partner who understands your company’s unique needs from day one. Fully integrated into the Scytale platform, so you can manage, track, and complete your audit – without the usual back and forth.

Simply integrate all your favorite tools to Scytale.

Control customization and gap analysis by our GRC experts.

Gap remediation, evidence collection and review.

Audit communication and findings. Audit report finalization.

AI-powered, continuous control monitoring and compliance.



“Working with Scytale was an accelerator for our company, helping us to stay focused on SOC 2 requests and pass the examination much faster than expected!”
Create a Trust Center in minutes so you can showcase your company’s security and compliance
Tune & align policies and procedures with our auditor-approved policy templates
Streamline your third party risk assessments with automated vendor risk management.
Automatically review user access data and get the evidence auto-collected for all relevant controls.
Identify and remediate any security and privacy gaps with our simplified risk assessment
Receive a list of controls customized to your organization
Easily achieve and maintain personnel-compliance training readiness
Leverage controls mapped from other security standards and regulations
Implement and manage your entire compliance process from prep to pass
Simply tag your colleagues and auditor in comments directly in Scytale




Timelines vary depending on your company’s size and maturity, and can take anywhere between a few weeks to 6+ months. Our platform is built to speed up the process with automation and dedicated expert guidance from audit-prep to official SOC 2 report, no matter the size of your organization.
Learn more about SOC 2 timelines here.
Nope! That’s exactly what we’re here for. Whether you’re an early-stage startup without a security or compliance hire or an enterprise with a full InfoSec team, we act as an extension of your internal resources. For startups, we’ll guide you from zero to compliant. For enterprises, we’re here to improve your existing processes, reduce overhead, and ensure scalability for 40+ frameworks and regulations.
Learn more about our compliance experts here.
SOC 2 costs vary based on your business stage, scope, and existing controls. We offer flexible pricing that scales with your needs – affordable for startups, predictable for growing companies, and efficient for large-scale teams.
And because we’ve built everything you need into one platform, like pen testing, a Trust Center, and full management of the audit process with your auditor, you won’t need to spend on extra vendors, tools, or consultants. Plus, we help you avoid costly mistakes by getting it right the first time.
Learn more about our pricing packages here.
You don’t need to worry about that, we’ll handle it. We’lll connect you with the right auditor based on your industry, company size, and timeline. With our Built-In Audit, you’ll align with your auditor from day one and get special bundle pricing for everything Scytale + your audit. We’ve built a strong audit network with top audit firms and know which ones are the best fit for fast-moving startups, scaling companies, or complex enterprise environments.
See all our audit partners here.
Eliminate all the compliance grunt work while closing more deals and building trust, faster than ever.