In this article, we’re looking at what SOC 2 controls are, and the role they play in becoming SOC 2 compliant.
Keeping track of your vendors doesn’t have to be daunting. Simplify all the moving parts with our automated vendor risk management.
Say goodbye to tedious, one-off vendor checks! With our Automated Vendor Risk Management, you get to automate the dull stuff like vendor onboarding, risk checks and mitigation, putting hours back on your clock.

“Scytale helped us consolidate our views to get a better understanding of our risk profile, our risk processes, and a path to success.”
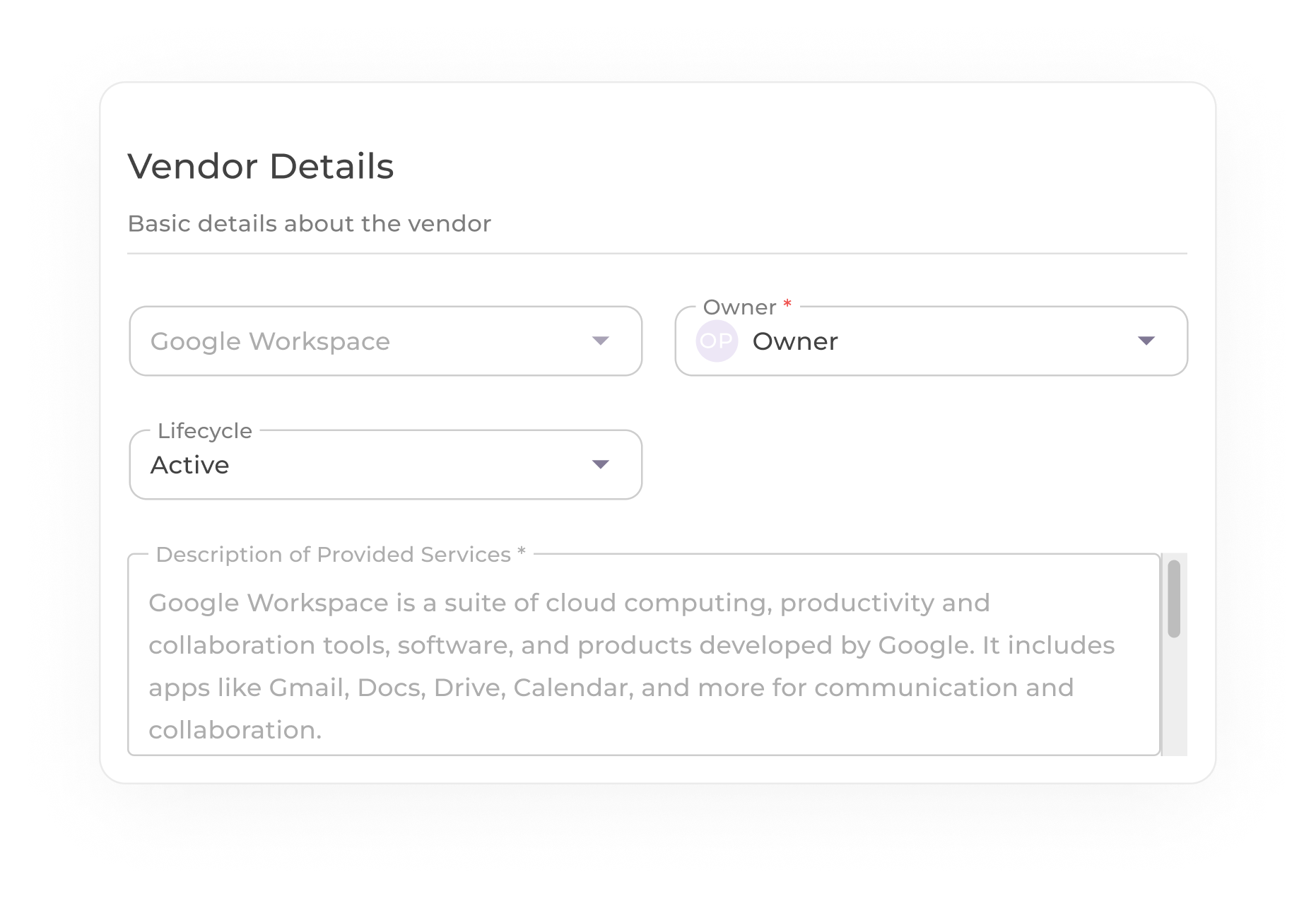
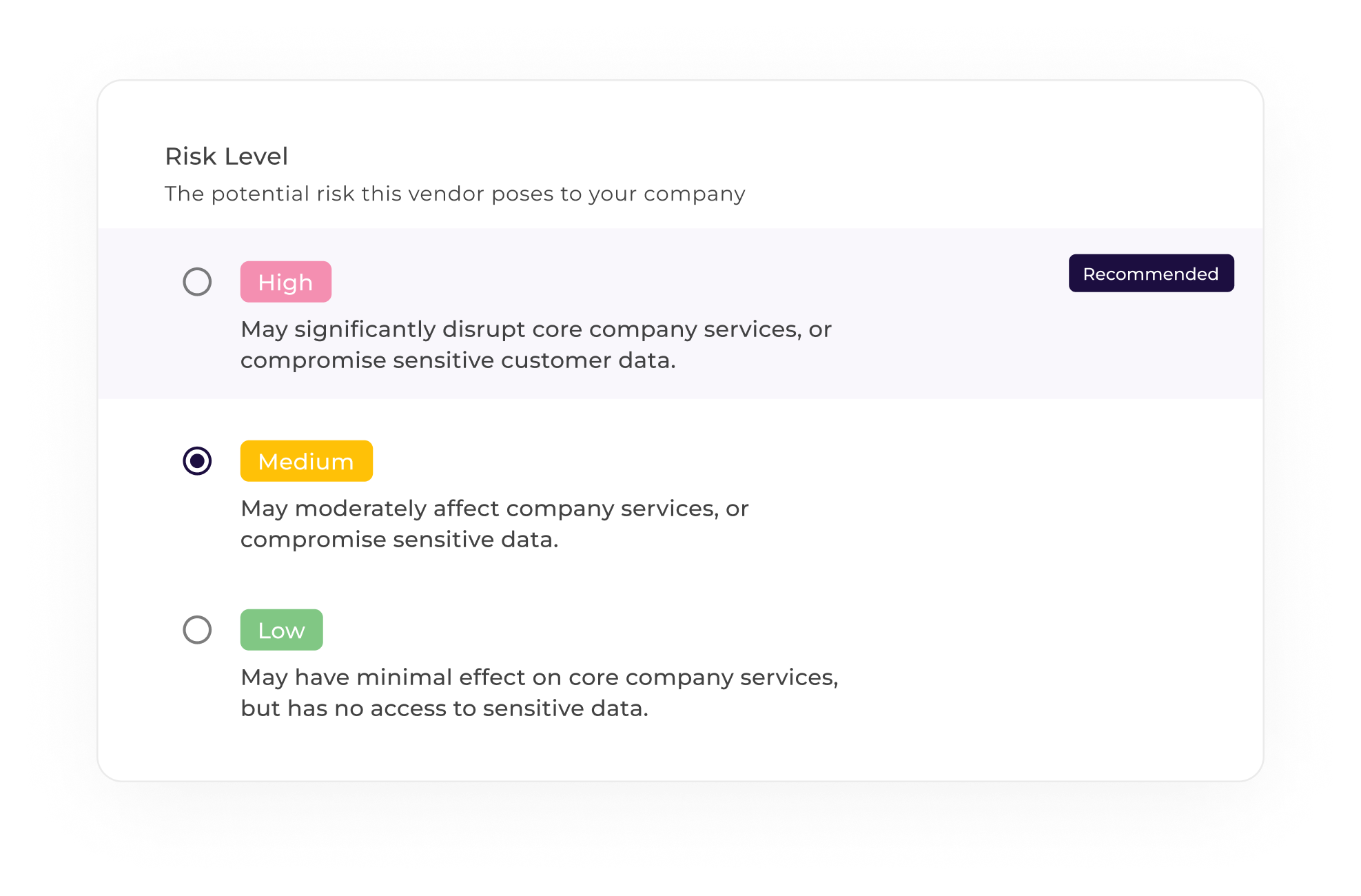
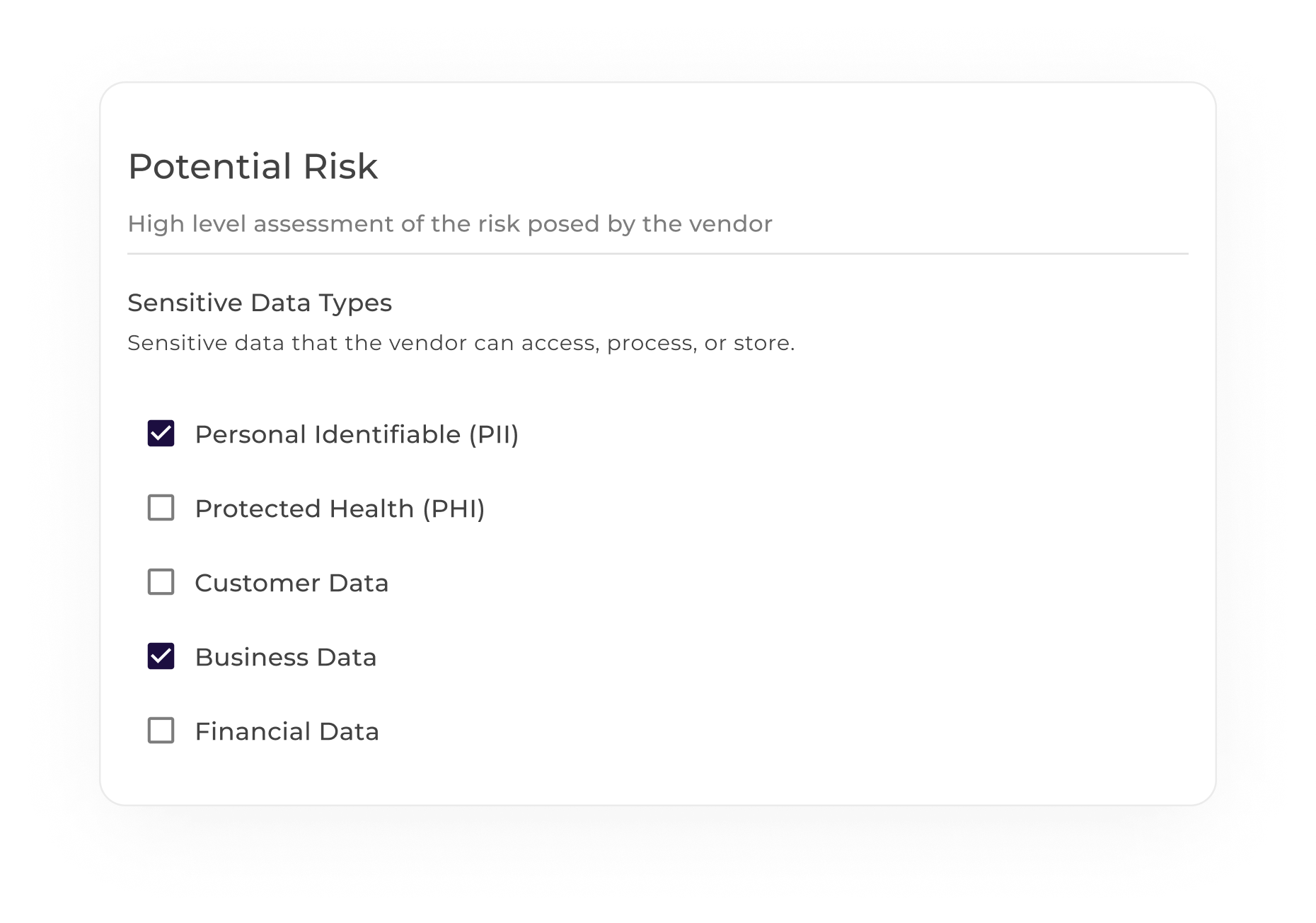
Forget about multiple spreadsheets and tools in order to conduct vendor risk assessments. Simplify this critical process with:
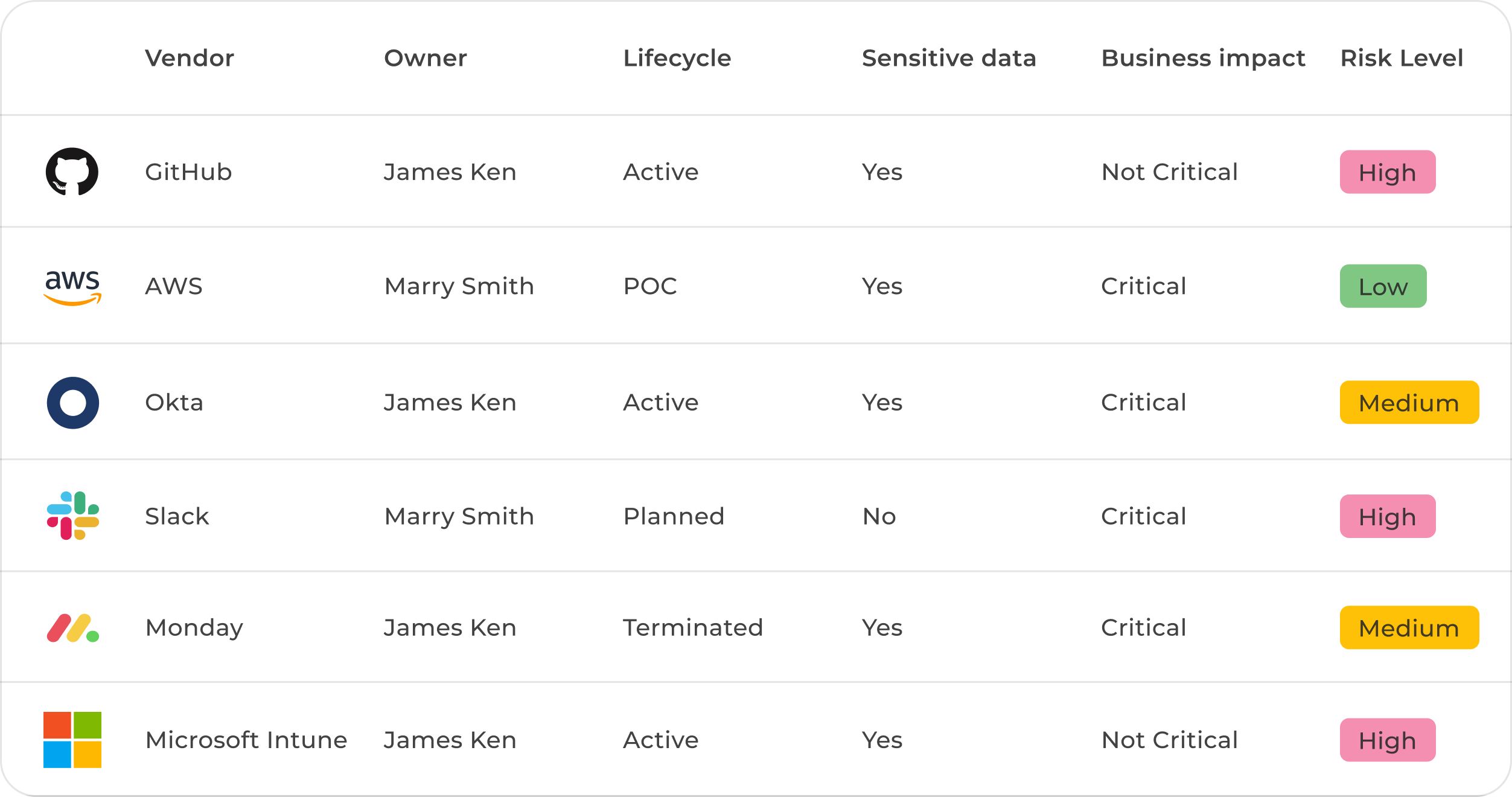
Accelerate your path to meeting and maintaining industry standards and regulations by centralizing and automating your vendor risk management.
Easily manage the risks associated with your vendors and have a clear overview of who you’re working with, optimizing risk management for today’s SaaS landscape.
Ensure a seamless integration into your existing risk management practices with our automated, personalized and flexible vendor risk management feature.

Ensure your risk management practices are in line with global standards, as our vendor risk feature supports the requirements of compliance frameworks.
More than a dozen security and privacy frameworks

Automate your audit-readiness process and boost customer trust by complying with the AICPA's Trust Services Criteria.

Meet the international gold standard and build your information security management system (ISMS) by streamlining compliance.

Ensure you're storing, managing and transferring protected health information (PHI) securely and automate your HIPAA compliance.

Comply with the European regulation on privacy and data protection by streamlining your compliance journey.
In this article, we’re looking at what SOC 2 controls are, and the role they play in becoming SOC 2 compliant.
If your business deals with sensitive data, it's important to understand the key differences between SOC 1 and SOC 2.
Scytale's DPO & Compliance Success Manager, Tracy Boyes, gives a brief breakdown of what is considered personal data under the GDPR.
Scytale's DPO & Compliance Success Manager, Tracy Boyes, outlines the key steps your organization needs to take to achieve GDPR compliance.
In this video, Scytale's DPO & Compliance Success Manager, Tracy Boyes, outlines the key roles in GDPR compliance.
Scytale's DPO & Compliance Success Manager, Tracy Boyes, talks about her extensive experience with GDPR and deep knowledge of the tech ...
Scytale's DPO & Compliance Success Manager, Tracy Boyes, discusses the significant impact a US federal law could have on privacy protection.
Scytale's DPO & Compliance Success Manager, Tracy Boyes, explains how Scytale can help your organization achieve compliance with the GDPR.
Scytale's DPO & Compliance Success Manager, Tracy Boyes, addresses whether vendors need to be HIPAA compliant if their customers are.
Raymond Cheng, experienced compliance auditor and CEO of Decrypt Compliance sits down with Scytale to discuss how to stay ahead of the game.
Take a look at Scytale's newest integrations added in 2024 including Deel, Hubspot, Asana, Cloudfare, and more.
Hear Scytale’s compliance expert Wesley Van Zyl and Cosmo Tech’s CIO, Jean-Baptiste Briaud discuss the ISO 27001:2022 updates in detail.
This guide will walk you through everything you need to know about CMMC compliance, from understanding the basics to achieving ...
This blog delves into CMMC, the introduction of CMMC 2.0, what's changed, and what it means for your business.
In this video, Aleksandra Klosowska explores how automation can streamline your compliance efforts and reduce manual workload.



