At first glance, becoming SOC 2 compliant can feel like navigating a complex maze. Sure, you’re aware of the necessity of ensuring that your organization protects customers’ data security, but in a constantly changing digital world, the security standards that organizations should adhere to are strict and non-negotiable. Clients are less likely to trust an organization that does not comply with a leading security standard like SOC 2.
In this article, we’re looking at what SOC 2 controls are, and the role your SOC 2 controls list plays in a SOC 2 audit, and ultimately, in becoming SOC 2 compliant. But before diving in, let’s quickly refresh some key terms you’ll see throughout the article.
TL;DR: SOC 2 Controls for Startups
- SOC 2 compliance proves that your SaaS startup protects customer data through structured, testable controls.
- The key benefits of SOC 2 compliance include stronger trust, smoother audits, and fewer security headaches.
- With Scytale, startups can leverage powerful automation, dedicated expert support, and Scy – an AI GRC agent – to streamline the SOC 2 compliance journey, saving valuable time and resources.
What is SOC 2?
SOC 2 is a reporting framework that can be considered the security blueprint for service organizations. Developed by the AICPA, especially for service organizations, this security compliance framework allows SaaS companies to verify that they meet what is considered peak-quality data security standards.
SOC 2 Controls
Your data security controls are the intentional tools and processes you’ve implemented into your organization to fulfill a specific security purpose. Let’s say you’re feeling somewhat tired and you’ve decided that you need to do something about it. The purpose is to re-energize yourself, the control may be to grab a cup of coffee. Alternatively, a control may be taking your daily vitamins, grabbing an energy drink, or perhaps catching up on some sleep. The same principle applies to SOC 2 controls.
In other words, SOC 2 is the overall security framework. SOC 2 controls are the measures, practices and processes taken to meet the organization’s SOC 2 objectives.
Security controls have become increasingly important for B2B SaaS companies, and if SOC 2 is part of your security compliance, implementing the necessary SOC 2 controls that apply to your organization is the essence of the SOC 2 compliance framework.
Having the necessary SOC 2 controls correctly implemented and operating effectively in your SaaS startup, you can ensure a robust security environment for your customers and compliance with SOC 2.
AICPA’s Trust Services Criteria
SOC 2 is guided by a list of five TSCs, Security, Availability, Processing Integrity, Confidentiality, and Privacy. Determining which TSC needs to be covered is a crucial part of preparing for your SOC 2 audit. However, the beauty of SOC 2 lies in its flexibility. Out of the five TSCs, it is only compulsory that your organization complies with the first category – Security.
As for the remaining TSCs, the intent of the flexibility of the SOC 2 framework is so that companies have the freedom to determine what criteria are beneficial and relevant to their customers that they plan to share the SOC 2 report with.
The Purpose of SOC 2 Controls
A SOC 2 control is the system or process that your organization implements in order to meet its SOC 2 compliance and information security objectives. The focus is on whether or not your organization fulfills predetermined objectives of control design and effectiveness within your selected TSC criteria. That being said, the natural first step is to know what these requirements are and to subsequently start implementing controls that not only align with these said requirements but that work best for your specific organization.
The Trust Services Criteria (TSC) Requirements
There are five Trust Services Criteria (formally called the Trust Services Principles) that make up the backbone of SOC 2. To become SOC 2 compliant, your organization needs to meet these requirements. As already mentioned, you do not have to meet all five criteria. Rather, each organization determines which TSCs are relevant and desirable, and then designs SOC 2 controls to achieve those goals. However, the first criterion, Security, is obligatory in all cases.
Within each TSC, there are specific multiple controls that can be tested.
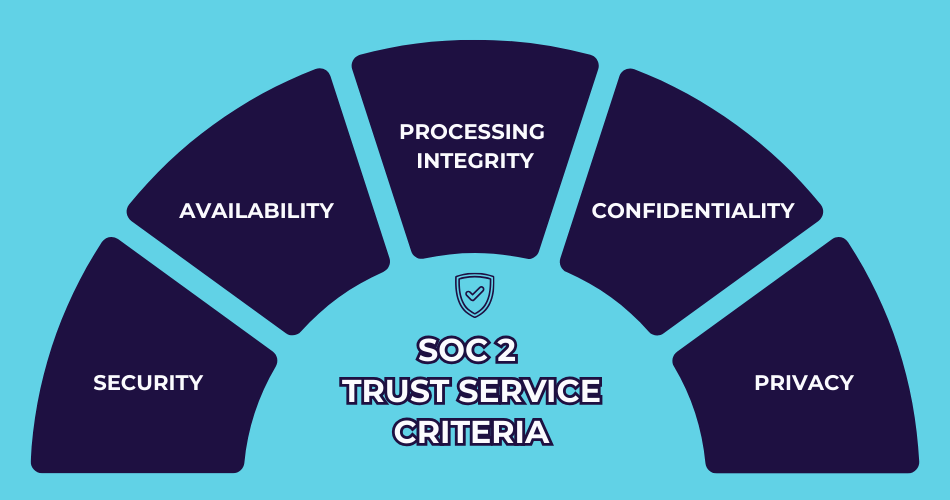
The Five SOC 2 TSC Requirements:
1. Security (mandatory)
The only obligatory requirement refers to the measures taken to protect against unauthorized access, unauthorized disclosure, and damage to systems.
Among the key areas covered by SOC 2 security controls are:
- Data Security: Ensuring that data is protected against unauthorized access (both physical and logical) throughout its lifecycle.
- Infrastructure: Establishing and maintaining secure infrastructure to support the SaaS offering, including networks, servers, and databases.
- Change Management: Implementing processes to manage changes to the SaaS environment in a controlled and secure manner, minimizing risks of disruptions and security breaches.
- Incident Response: Having procedures in place to detect, respond to, and recover from security incidents effectively, thereby minimizing impact on customers.
2. Availability
Information and systems are available for operation and use.
3. Processing Integrity
System processing is complete, valid, accurate, timely, and authorized.
4. Confidentiality
Information designated as confidential is protected.
5. Privacy
Personal information is collected, used, retained, disclosed, and disposed of appropriately.
To understand the full extent of SOC 2 and how to determine the scope of your SOC 2 audit, it’s important to understand the Trust Services Criteria and how they can assess the risk and opportunities associated with the information security of an organization.
SOC 2 Security Controls List: The Common Criteria Controls
As mentioned earlier, organizations are given full autonomy over which TSC they develop controls for as well as what those controls consist of.
Perhaps confidentiality and availability are some of your organization’s core principles and operations. Your organization would prioritize developing all necessary controls for these TSCs. In short, your organization only implements the controls that are relevant to its operations, under the TSC included in your SOC 2 scope. However, the one TSC that isn’t optional, is Security.
Security controls are essential and an obligatory requirement for all service organizations, which is why we’d like to focus on some controls to keep in mind when developing your controls list, relating to Security.
Logical (Technical) and Physical Access Controls
This refers to the application of technical and physical safeguards. Its primary purpose is to protect information assets through security software, data encryption, infrastructures, or any other access control that best fits your organization. Within a SaaS company, the primary purpose of logical access controls is to authenticate and authorize access within computer information systems.
Authentication is a widely-accepted logical access control. However, as technology advances, it’s safe to assume that traditional password authentication doesn’t cut it anymore. With greater threats constantly developing within cybersecurity, password authentication lacks a strong enough identity check.
With each passing year, authentication strategies are becoming more complex, and more advanced protocols and processes are preferred among service organizations. This allows greater certainty in the identity of those who access system resources.
Examples of logical access controls:
- Network firewalls
- Passwords with two-step verification
- Intrusion detection systems
- Data encryption
Examples of physical access controls:
- Perimeter security
- Employee verification
- CCTV systems
- Physical or electronic locks
Change Management Controls
The change management process is considered a part of the IT general controls in any service organization. It includes standardized processes that authorize, regulate and approve any and all changes made to data, software, or infrastructure. It also includes analyzing and confirming whether or not each change is meeting its predetermined objectives.
Examples of change management controls:
- Branch controls in code repositories
- Human review & approval prior to pushing a change to production
- Static/dynamic tests prior to release to production.
System Operation Controls
Can you accurately detect and identify new vulnerabilities? Is there any deviation or abnormalities, and do you have a system in place to detect and mitigate any and all risks associated? These controls refer to the consistent monitoring of any changes within the service organization that may lead to fresh vulnerabilities.
Examples of system operation controls:
- Incident response protocols
- Threat detection
- Root cause analysis
A popular and comprehensive outsourced program that is frequently used as a control for system operation is managed detection and response (MDR), which covers all of the above.
In closing, it’s important to understand that although SOC 2 controls may not seem as straightforward to implement as one may wish, it is ultimately to benefit the security of the organization. However, that doesn’t mean that you’re left in the dark when it comes to implementing the right SOC 2 controls – not if we can help it.
SOC 2 Controls and TSC: What Startups Need to Know
When people talk about a list of SOC 2 controls, they’re really referring to the controls mapped against the Trust Services Criteria. There isn’t a single universal checklist that fits every SaaS company. Instead, your SOC 2 controls should match your business environment and the unique risks you face. This is why many startups build their own tailored SOC 2 control list as part of the audit prep.
Here’s a simple table showing how SOC 2 controls align with the Trust Services Criteria (TSC) framework:
| Trust Services Criteria (TSC) | SOC 2 Controls Examples |
|---|---|
| Security (mandatory) | Firewalls, multi-factor authentication (MFA), intrusion detection, regular vulnerability scans |
| Availability | Backup systems, disaster recovery plans, uptime monitoring, redundancy in infrastructure |
| Processing Integrity | Transaction validation, error detection tools, automated reconciliation, input/output checks |
| Confidentiality | Data classification policies, role-based access controls, encryption for data at rest and in transit |
| Privacy | Consent management processes, data minimization practices, secure data disposal, privacy notices for customers |
By expanding controls in each category, SaaS startups can see concrete examples that map directly to the Trust Services Criteria. This makes it easier to identify which controls are relevant to their operations while avoiding unnecessary overhead.
The flexibility of SOC 2 means you only need to apply the list of SOC 2 controls that matter most to your customers and business model.
GET SOC 2 COMPLIANT 90% FASTER
Benefits of SOC 2 Compliance for SaaS Companies
For companies to prove they’re serious about protecting customer data and running a tight ship, SaaS companies especially often pursue SOC 2 compliance, offering several significant advantages:
- Enhanced Trust and Credibility: SOC 2 compliance demonstrates to customers that the company takes data security seriously and has implemented appropriate controls to protect their information.
- Competitive Edge: In a crowded market, SOC 2 compliance can serve as a differentiator, giving potential customers confidence in the security and reliability of the SaaS product.
- Regulatory Compliance: Many industries and regulatory frameworks require SaaS providers to demonstrate adherence to specific security standards. This is especially relevant for businesses providing age verification services, where compliance with data security regulations is critical to protecting user information.
- Operational Efficiency: Implementing SOC 2 controls often leads to improved operational processes and efficiencies, reducing the likelihood of disruptions and improving overall service delivery.
The SOC 2 Compliance Process: Steps for Startups
Achieving SOC 2 compliance involves several steps, including:
- Assessment: Conducting an initial assessment of current controls and identifying gaps.
- Remediation: Addressing identified gaps by implementing necessary policies, procedures, and technologies.
- Audit: Engaging a qualified third-party auditor to assess the effectiveness of implemented controls against SOC 2 criteria.
- Reporting: Upon successful completion of the audit, receiving a SOC 2 report (either Type I or Type II) that details the scope, controls, and auditor’s opinion.
SOC 2 Compliance Software for SaaS Companies
As you’re probably aware, there are no shortcuts or easy formulas you can copy and CTRL+V when it comes to SOC 2 compliance. However, when it comes to implementing the right controls, we’ve got you covered! Our SOC 2 superhero team develops a controls list customized to your organization and advises why it is best to include some and leave some out of your scope.
Manual compliance can be costly, tedious, time-consuming, and frequently contain human error. Some risks just aren’t worth taking. With the right SOC 2 automation software, a dedicated team of GRC experts, and our AI GRC Agent – Scy – on your side, you’ll benefit from a guided risk assessment and tailored controls based on your company’s needs.
At Scytale, we believe that with an intentional strategy, AI-driven automation, and professional input on where to focus (and what to avoid), you can simplify SOC 2 and save hundreds of hours on compliance.
🎙️ Want a fresh take on SOC 2? Check out our podcast episode below to hear how startups are finding creative ways to make compliance more engaging.
Don’t just take our word for it. See how we’ve done this for our customers!
FAQs about SOC 2 Controls and Compliance
What is SOC 2 compliance for startups?
SOC 2 compliance shows your startup can protect customer data with strong security practices. It builds trust with clients, helps win deals, and makes your SaaS company look professional and enterprise-ready.
What is SOC 2 compliance for SaaS?
SOC 2 compliance proves a SaaS company securely handles customer data. It reassures clients that controls are in place for data protection, availability, and privacy, making it easier to close enterprise contracts.
How many controls are there in SOC 2?
SOC 2 doesn’t have a fixed number of controls. Instead, it uses the five Trust Services Criteria (TSC). Each organization tailors its own controls list to meet the criteria relevant to its services; however, it’s important to note that Security is mandatory.
What is the SOC 2 control list?
The SOC 2 control list is a collection of processes and safeguards a company adopts to meet SOC 2 audit requirements. It may include security tools, monitoring systems, access controls, and response procedures.
Why are SOC 2 controls important?
SOC 2 controls protect sensitive data, prevent data breaches, and prove to customers that your business takes security seriously. They’re the backbone of compliance and critical for trust in SaaS.