You need to undergo ISO 27001 compliance but don’t know how it all works? We get it. There are so many details to take into consideration and figuring out where exactly to even start is all so common, especially for startups just starting their security compliance journey. We know you have probably googled ‘ISO 27001’ and the overwhelmingly amount of information is enough to make you start panicking.
Undergoing ISO 27001 compliance, especially for the very first time, can cause a few nightmares, to say the least. With so many requirement boxes to tick and ensuring you do it all correctly, can be quite the task at hand. And that’s where an ISO 27001 checklist comes in.
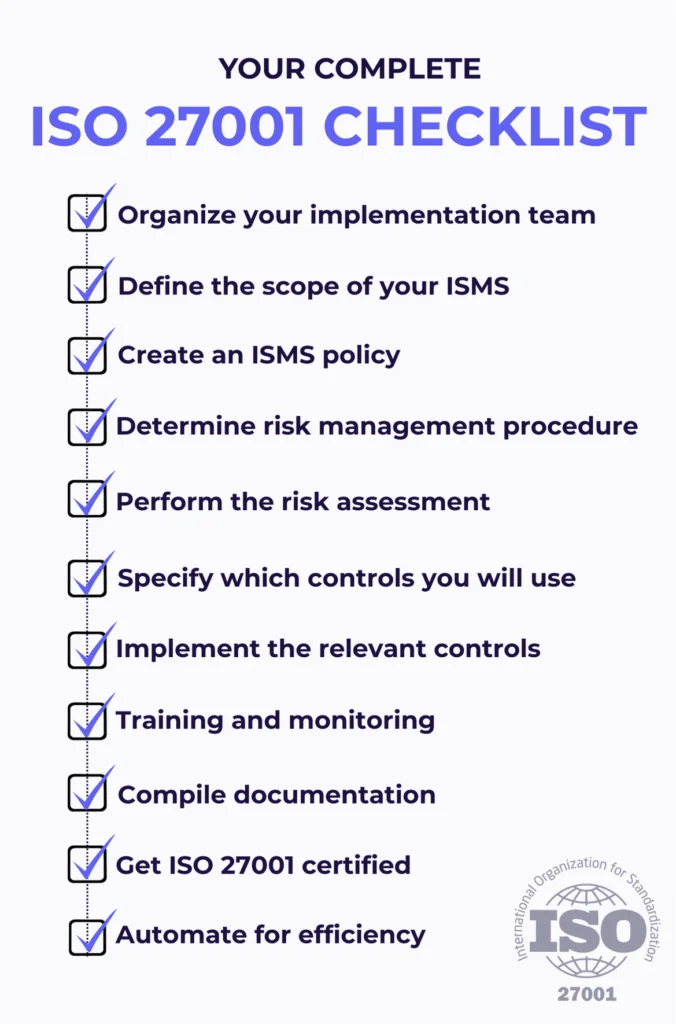
If you want to implement ISO 27001 successfully, you need to ensure you’ve covered all your bases. We’ve compiled an ISO 27001 checklist to help you develop an effective ISO 27001 strategy and undergo a successful certification process.
Look at this as your very own ‘go-to’ source of information you can turn back to anytime.
TL;DR: ISO 27001 Checklist
- ISO 27001 certification ensures effective data security management, helping you maintain a strong security posture at all times.
- The process involves key steps like defining the ISMS scope and assessing risks.
- Clear documentation, security awareness training, and continuous monitoring are essential for success.
- Compliance automation software streamlines ISO 27001 processes, reducing manual work and automating key tasks like evidence collection, user access reviews, and vendor risk management, all while boosting efficiency and accuracy.
- Scytale’s AI-powered platform accelerates your ISO 27001 journey with seamless automation, expert guidance from GRC professionals, and Scy, Scytale’s next-gen AI GRC Agent, ensuring a faster, more efficient compliance process.
What is an ISO 27001 compliance checklist?
So, what exactly is an ISO 27001 compliance checklist you may ask?
In short, an ISO 27001 checklist is a summarized ‘to-do’ list to guide organizations on their ISO 27001 certification journey, providing all the main steps they need to take in order to ace their ISO 27001 certification audit and have full peace of mind that there are no roadblocks, surprises or key aspects missing. With that being said, another good term to use is an ‘ISO 27001 requirements checklist.’
Why you need an ISO 27001 compliance checklist
ISO 27001 is one of the best ways to bulletproof your company’s data security. As a leading international standard, ISO 27001 certification is always an excellent way to gain a competitive advantage. Potential partners and customers are immediately reassured that your company provides secure, reliable, quality service.
However, there’s a reason ISO 27001 is such a prized standard. It’s a framework that offers significant benefits and covers all relevant vulnerabilities across your organization.
When implementing such a comprehensive protocol, you want to ensure that no critical details are overlooked, so it’s vital to use an ISO 27001 audit checklist.
Get ISO 27001 compliant 90% faster
Which documents are required for ISO 27001 certification?
To achieve ISO 27001 certification, several mandatory documents must be in place. These documents help demonstrate that your organization has implemented the necessary information security management controls and that they are working effectively.
Having the right compliance documentation not only supports your path to ISO 27001 certification but also ensures you’re continuously managing risks and protecting sensitive data in line with global best practices.
Let’s take a look at some of the key documents you’ll need to prepare:
- Information Security Policy: This is a high-level document that outlines your organization’s commitment to information security. It includes the purpose and objectives of the ISMS, and acts as a roadmap for defining the company’s security objectives. This policy sets the tone for how the entire organization handles information security.
- Risk Assessment and Treatment Plan: These documents are crucial for evaluating risks and defining how they will be mitigated. The risk assessment identifies potential security threats and vulnerabilities, while the treatment plan outlines how each risk will be addressed – whether it’s by reducing, avoiding, sharing, or accepting the risk. Both documents form the core of your organization’s proactive approach to managing information security.
- Statement of Applicability (SoA): The SoA details which security controls are applicable to your organization, according to ISO 27001’s Annex A controls. This document is vital for defining what’s included in your ISMS and why certain controls might not be applicable. It also helps demonstrate the rationale for your control selections, making it a key element of your certification.
- Procedures for Internal Audit and Management Review: ISO 27001 internal audits ensure that the ISMS is functioning as planned, helping identify gaps and areas for improvement. A management review ensures that the ISMS is continually improved by reviewing audit results and feedback. These procedures are essential for maintaining the integrity of your ISMS over time.
- Risk Assessment Methodology: This document explains how your organization evaluates risks consistently. It includes the criteria for deciding whether a risk is acceptable or needs to be addressed, and outlines how those decisions are made. It ensures that risks are assessed in a clear, standardized way.
- Evidence of Security Awareness and Training: Records of security awareness training are important for ISO 27001. They show that all staff understand their role in maintaining security. Ongoing training helps ensure the organization is ready to handle security challenges and that everyone stays up to date on best practices.
- Control Implementation Records: These documents prove that security controls, like technical controls for example, have been properly implemented and are working as expected. They are crucial for showing auditors that the controls you’ve put in place are managing the identified risks and that the ISMS is running smoothly.
💡 These documents are crucial to the ISO 27001 certification process. They ensure your ISMS is solid, comprehensive, and fully aligned with ISO 27001 standards. Beyond preparing you for the audit, they lay the groundwork for building a lasting, proactive information security strategy that keeps improving as your business grows.
The official ISO 27001 checklist
Now, let’s get to the real reason you’re here and dive into what’s required to get ISO 27001 certified. This checklist will help ensure you’ve covered all your ISO 27001 bases.
1. Organize your implementation team
Get leadership actively involved
Making sure senior management is actively involved is the first step for a reason. Strong leadership will play a huge role in determining the success of your ISO 27001 process.
Appoint an ISO 27001 project manager
Step two is to appoint an ISO 27001 manager to drive the project. If necessary, you may need to create a dedicated implementation team.
These two steps are connected. Your ISO 27001 team needs the full backing and support of leadership. They need sufficient authority to make all necessary decisions and interventions. And they need adequate resources to effectively run the process.
Assign roles and responsibilities
ISO 27001 will involve personnel from across the organization. Everyone needs to be clearly briefed on their duties and responsibilities. In order for the process to be successful, you need clear lines of communication. To streamline implementation, many companies rely on compliance technology to manage workflow and help coordinate roles.
2. Define the scope of your ISMS
Defining the scope of your Information Security Management System (ISMS) is one of the most important data security questions.
It is critical that your scope is sufficiently broad to cover all critical security risks. If your scope is too narrow, there could still be critical gaps in your information security protocol.
On the other hand, defining the scope too broadly is a waste of time and resources. Getting the balance right and ensuring it’s relevant to your specific organization is a key strategic decision.
3. Create an ISMS policy
The information security management system (ISMS) policy defines your high-level data security needs and objectives.
The document is the blueprint that will shape leadership’s vision for defining and implementing information security across the organization. At this point you should draw up your ISO 27001 documentation templates and share policies with all stakeholders.
4. Determine your risk management procedure
ISO 27001 doesn’t specify how you should score risks. Each organization must make a decision about which metric they will use. You need to decide upfront whether you are going to use a qualitative or quantitative metric. However, you should customize your approach to the needs of your organization. Once you have made a decision, all relevant personnel must be fully briefed on the risk management protocol.
5. Perform the risk assessment
An ISO 27001 risk assessment helps organizations identify, analyze and evaluate gaps in their information security practices. Once you have chosen an assessment methodology, you can apply it to the actual risk assessment. This process involves carefully identifying potential risks to the organization. However, this is only the first step. You also need to evaluate those risks. That process comprises two major components, assessing risk impact and devising a risk treatment plan.
Assessing risk impact
Assess the consequences of each risk. Some vulnerabilities could have a very high impact and thus are a priority. Other vulnerabilities may have a low impact, and thus may be a lower priority.
Implement a risk treatment
At this point, you need to decide how you will address all the security vulnerabilities that you have identified. Your response to each will be informed by the risk assessment.
In terms of the ISO 27001 protocol, there are four recognized actions you can take to address each unacceptable vulnerability. These include:
- Decrease the risk
- Avoid the risk
- Share the risk
- Retain (accept) the risk.
6. Specify which controls you will use
At this point you have identified risks, and decided what kind of action you will take to address each of them.
The process will help you choose and implement the appropriate ISO 27001 controls. Draw up a Statement of Applicability (SoA) detailing which controls are relevant and which controls are not applicable.
It is helpful to describe why each control does or does not apply to your organization’s ISO 27001 program.
7. Implement the relevant controls
This step sounds obvious, for what’s the point of working so hard to identify and assess risk unless you’re actually going to address those risks, as well as implement best information security practices?!
However, implementation isn’t just about ticking boxes and issuing policies. It’s also about getting everyone on board, and driving new ways of working. If your team doesn’t actually change their work behavior, then you haven’t yet successfully implemented ISO 27001 controls.
8. Training and monitoring
Once we understand that implementation depends on real, effective change, we can appreciate the need for continuous control monitoring. The greatest ISO 27001 strategy doesn’t amount to much if it is not implemented effectively. Ongoing monitoring lets you know that your controls are effective, and that they continue to be effective. This is what your customers want to see.
At the same time, effective change is only possible if all stakeholders understand what to do and when to do it. Ongoing training and support is, therefore, a core part of the implementation process.
9. Compile documentation
Before you undergo an audit, you need to collect as much evidence as possible. The more detailed documents you can compile, the better your audit outcomes are likely to be.
In the past, collecting and collating large volumes of data was an extremely time-consuming, error-prone and tedious task. Fortunately, automation is redefining compliance management processes, making the entire process faster, more efficient, and eliminating the risk of human error.
10. Get ISO 27001 certified
It’s time for the main event. In order to become ISO 27001 certified, a suitable independent auditor must assess your ISMS and, hopefully, issue certification.
If you have carefully followed the preceding steps, your chances of success will be much higher. This is important because the audit process is time-consuming and costly regardless of whether your audit is successful. So it pays to take the time and care to get it right the first time.
11. Automate for efficiency
With such a detailed process to follow and serious strategic decisions to make, how can you keep track of the entire ISO 27001 process without missing anything important? The answer is simple: automation.
The latest in compliance technology, like Scytale‘s AI-powered automation platform, is transforming how businesses manage GRC.
Our ISO 27001 automation platform ensures continuous security awareness for all employees, automates critical tasks like evidence collection and risk assessments, maintains ongoing compliance, and provides a fully customizable Trust Center that enables you to easily showcase your security and compliance posture.
Plus, with tailored guidance from dedicated GRC experts and Scy, our next-gen AI GRC agent, you’re never alone in navigating your compliance journey.
By leveraging ISO 27001 compliance software, becoming and staying compliant becomes faster, smoother, and more affordable. This means more businesses can now enjoy the numerous advantages of ISO 27001 certification.
Don’t just take our word for it — take a look at what our customers have to say about streamlining their compliance processes!
Achieving ISO 27001 certification is a major milestone, but it’s just the beginning. Establish a continuous improvement cycle to keep strengthening your Information Security Management System (ISMS). Regularly review and update your risk assessments, controls, and policies to stay ahead of evolving threats and industry changes. This proactive approach ensures your organization maintains business continuity and is always ready to tackle any security challenge that arises.
FAQs about the ISO 27001 Checklist
What is the ISO 27001 checklist?
The ISO 27001 checklist is a guide that outlines the steps needed to achieve ISO 27001 certification. It includes all the necessary activities, documentation, and controls to help businesses of all sizes achieve information security compliance. With tools like Scytale’s AI-powered compliance automation platform, businesses can streamline this process, making it faster and more efficient while ensuring they stay on track to meet all ISO 27001 requirements.
What are the ISO 27001 requirements?
ISO 27001 requires organizations to implement an Information Security Management System (ISMS) that covers risk assessments, security controls, documentation, and continuous monitoring to ensure the protection of sensitive data.
Is the checklist required for certification?
While the checklist is not mandatory, it serves as a helpful guide to ensure your organization meets all ISO 27001 compliance requirements. Following it makes it easier to stay on track and helps your business successfully achieve and maintain ISO 27001 certification.
Are there mandatory items in the ISO 27001 checklist?
Yes, certain items are mandatory for ISO 27001 certification, including a risk assessment, Statement of Applicability (SoA), and security controls implementation. These documents are essential for demonstrating compliance. Scytale’s dedicated GRC experts can provide tailored guidance throughout this process, ensuring your organization meets all mandatory requirements and stays on track for certification.
For how long is an ISO certification valid?
ISO 27001 certification is typically valid for three years. However, ongoing audits and reviews are required to maintain compliance throughout the certification period.





