TL;DR: SOC 2 compliance for SaaS
- SaaS companies use SOC 2 to demonstrate strong security controls, which are often required during vendor security reviews.
- SOC 2 reports include Type I, which evaluates control design at a point in time, and Type II, which assesses performance over time.
- Preparing for SOC 2 requires defining scope, implementing controls, documenting policies, and completing an audit.
- SaaS environments present challenges like complex cloud infrastructure, rapid release cycles, and the need for effective multi-tenant data management.
- Scytale stands out as a leading SOC 2 compliance platform that helps automate evidence collection and streamline audit preparation.
A potential customer asks for your SOC 2 report during the procurement process. Your team does not have one in place, and the deal slows while security questionnaires, vendor risk assessments, and documentation requests begin to accumulate.
Organizations of all sizes, from fast-growing SaaS startups to well-established enterprises, encounter this situation as they begin working with larger customers and partners. What was once viewed as a future security initiative quickly becomes a critical requirement for accelerating sales cycles and demonstrating that customer data is protected through structured security controls.
In this article, you’ll learn what SOC 2 is, why SaaS companies need it, and how organizations become SOC 2 compliant.
What is SOC 2?
SOC 2 stands for System and Organization Controls 2. It is a voluntary U.S. compliance framework developed by the American Institute of Certified Public Accountants (AICPA) that helps organizations demonstrate they have effective controls in place to protect customer data.
The SOC 2 framework evaluates how organizations protect customer data across their systems, technology, and operational processes to reduce the risk of security incidents. Auditors assess these controls using the Trust Services Criteria (TSC), which include Security, Availability, Processing Integrity, Confidentiality, and Privacy. SOC 2 compliance is widely adopted by SaaS companies and other organizations that handle sensitive customer data, helping demonstrate that effective controls are in place to protect it.
SOC 2 reports are issued in two formats:
- Type I: Reviews the design of controls at a specific point in time.
- Type II: Reviews how those controls operate over a defined period (typically several months).
Most SaaS organizations opt for Type II reports because they demonstrate that controls operate consistently across the organization’s environment.
Why do SaaS companies need SOC 2?
Many enterprise buyers require a SOC 2 report as part of vendor security reviews and third party risk assessments. Providing a current SOC 2 report helps organizations demonstrate that appropriate security controls are in place to protect sensitive customer data.
SOC 2 compliance can also help accelerate sales cycles. With a validated report available, sales and security teams can respond to security questionnaires and procurement reviews more efficiently, reducing delays during the buying process.
Investors increasingly expect growing SaaS companies to demonstrate strong security governance, particularly during fundraising and due diligence. In crowded SaaS markets, SOC 2 also serves as a key competitive differentiator by providing independent verification of an organization’s security practices.
Is SOC 2 legally required for SaaS?
SOC 2 is not a legal requirement for SaaS companies. There’s no regulation that mandates obtaining a SOC 2 report before operating or selling software. However, it has become a widely expected standard, especially when selling to larger organizations.
It’s also important to note SOC 2 is often referred to as a “certification,” however it’s actually an attestation report issued by an independent third-party auditor. This report confirms that security controls are functioning as intended, serving as a trusted seal of approval for SaaS companies to meet market expectations and build long-term customer trust.
Which SOC 2 Trust Services Criteria apply to SaaS?
The SOC 2 framework includes five Trust Services Criteria (TSC) that address different aspects of security and operational control within a SaaS environment. Organizations determine which criteria fall within the SOC 2 audit scope based on product architecture, customer requirements, and how data is handled.
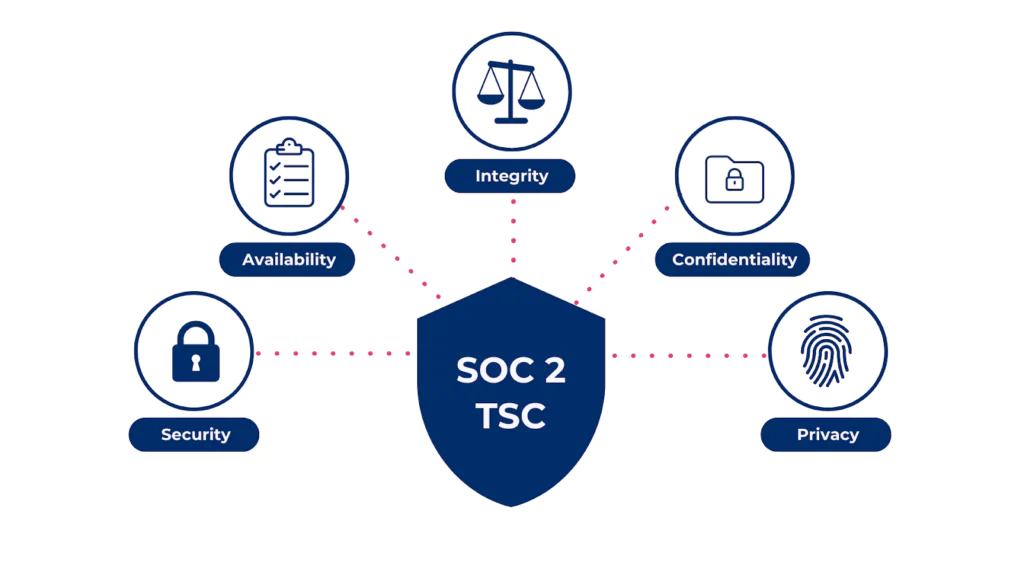
1. Security
Security is the only mandatory principle out of the five SOC 2 principles. It forms the foundation of every SOC 2 audit, focusing on protecting systems from unauthorized access. SaaS companies typically implement identity management, access controls, infrastructure monitoring, and incident response processes to meet this requirement.
2. Availability
Availability evaluates whether systems remain operational and accessible according to service commitments. SaaS platforms address this through uptime monitoring, infrastructure redundancy, disaster recovery planning, and incident management procedures.
3. Processing Integrity
Processing integrity applies to SaaS products that process or transform customer data. Controls focus on ensuring system processing is accurate, complete, and authorized.
4. Confidentiality
Confidentiality addresses the protection of sensitive information within the platform. SaaS companies support this through encryption, access restrictions, data classification, and secure storage practices.
5. Privacy
Privacy applies when organizations collect or process personal data. Companies align internal policies and controls with principles governing data collection, use, retention, and disclosure.
Get SOC 2 Compliant 90% Faster
SOC 2 Type I vs. Type II: Which should a SaaS company start with?
SOC 2 Type I and Type II reports support different stages of a SaaS security program. The key difference lies in how auditors evaluate your controls.
SOC 2 Type I:
A SOC 2 Type I report evaluates whether your security controls are properly designed at a specific point in time. For many SaaS companies, this is the fastest way to show that the necessary security and compliance processes are in place, helping support early enterprise sales conversations.
Startups and growing SaaS companies often begin with Type I when they need to respond to customer security questionnaires or procurement reviews but have not yet operated their controls long enough to complete a longer audit period.
SOC 2 Type II:
A SOC 2 Type II report goes further by evaluating how those controls operate over time, typically across several months. This provides stronger assurance that security processes are not only properly designed but also consistently followed across the organization.
As SaaS companies scale and begin working with larger enterprise customers, most transition to Type II, as it is widely expected during vendor security assessments and third-party risk reviews.
How does SOC 2 compare to other frameworks for SaaS?
SOC 2 often forms part of a broader compliance strategy for SaaS companies. As organizations scale, they may adopt additional frameworks based on compliance requirements, the types of data they process, and customer or market expectations.
SOC 2 vs. ISO 27001
ISO 27001 is an international information security standard focused on establishing and maintaining an Information Security Management System (ISMS). SOC 2 offers an independent auditor’s report on security controls, while ISO 27001 provides a formal certification recognized globally.
SOC 2 vs. GDPR
GDPR governs how organizations collect, process, and protect personal data belonging to individuals in the European Union. Unlike SOC 2, which evaluates operational security controls, GDPR is a regulation focused on privacy rights and data protection obligations.
SOC 2 vs. SOX ITGC
SOX ITGC is a regulation that supports the integrity of financial reporting for public companies. SOC 2 focuses on protecting customer data and operational security, while SOX ITGC ensures that financial systems and processes maintain proper control and auditability.
What are the biggest SOC 2 challenges for SaaS companies?
SaaS platforms operate in environments that introduce unique operational and security complexities for SOC 2 compliance. As a result, organizations often encounter several key challenges:
Cloud infrastructure complexity in SaaS environments
Most SaaS platforms rely heavily on cloud infrastructure, which introduces complexity when managing security controls. Teams must maintain proper access permissions, logging, monitoring, and network configurations across multiple cloud services to meet SOC 2 requirements.
Fast release cycles and continuous software deployment
SaaS companies often deploy product updates frequently as part of modern development practices. Without structured change management and review procedures, maintaining consistent security oversight during rapid release cycles can be challenging.
Multi-tenant architecture and customer data separation
SaaS platforms typically store and process data from multiple customers within the same environment. Organizations must demonstrate strong logical separation of tenant data through access restrictions, encryption, and infrastructure controls.
Distributed teams and remote access management
Many SaaS companies operate with distributed or fully remote teams. This requires strong identity management, endpoint security, and clearly documented onboarding and offboarding processes to maintain consistent security controls.
Heavy reliance on third-party vendors
SaaS platforms frequently depend on external vendors for infrastructure, monitoring, analytics, and support services. These dependencies require structured vendor risk management processes to assess vendor security posture and maintain oversight of third-party access to systems and data.
How do SaaS companies get SOC 2 compliant?
SaaS organizations follow a structured GRC process to prepare for a SOC 2 audit. The steps below serve as a practical SOC 2 compliance checklist for teams preparing for their first audit and maintaining continuous compliance.
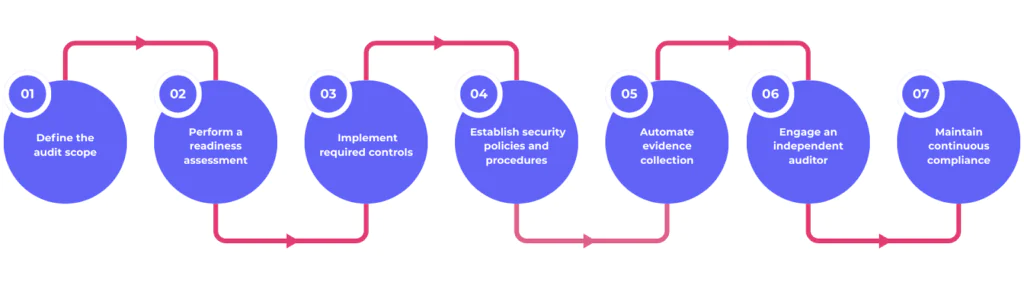
Step 1: Define the SOC 2 audit scope
Organizations begin by identifying the systems, infrastructure, and services included in the SOC 2 audit. This usually covers production environments, supporting cloud services, and key operational processes.
Step 2: Perform a SOC 2 readiness assessment
A readiness assessment evaluates the current security posture against SOC 2 requirements. This process identifies control gaps and areas requiring stronger governance or technical safeguards.
Step 3: Implement SOC 2 controls
Security and engineering teams implement controls needed to meet SOC 2 criteria. Common SOC 2 controls include access management, infrastructure monitoring, incident response procedures, and change management processes.
Step 4: Establish SOC 2 policies and procedures
SOC 2 requires documented compliance policies that define how security operations are managed. These policies typically address areas such as access controls, risk management, incident response, vendor oversight, and employee security practices.
Step 5: Automate evidence collection
Auditors require evidence showing that controls operate as intended. SOC 2 automation platforms help collect logs, configurations, approvals, and monitoring records directly from cloud systems and security tools.
Step 6: Engage an independent SOC 2 auditor
Once controls are implemented and operating effectively, organizations engage a licensed auditing firm. The auditor evaluates the controls and issues the formal SOC 2 attestation report.
Step 7: Maintain continuous compliance
SOC 2 compliance demands continuous monitoring, requiring organizations to uphold controls across infrastructure, development workflows, and operational processes to ensure audit readiness and maintain SOC 2 compliance.
How long does SOC 2 take for a SaaS company?
SOC 2 timelines vary depending on the maturity of an organization’s security program and the complexity of its engineering environment. Many SaaS companies reach SOC 2 Type I readiness within 2-4 months, which typically includes defining audit scope, establishing policies, implementing controls, and preparing documentation for review.
SOC 2 Type II requires an observation period during which auditors evaluate how controls operate over time, usually lasting 3-12 months. Top compliance automation tools can help accelerate readiness by organizing controls, centralizing compliance documentation, and automating evidence collection across cloud infrastructure and security systems.
How much does SOC 2 cost for SaaS companies?
SOC 2 compliance costs vary based on company size, infrastructure complexity, and audit scope. Most SaaS companies budget across three main areas: audit fees, compliance software, and internal operational effort.
Audit firms typically charge $15,000 to $40,000 for a SOC 2 engagement, influenced by factors such as the organization’s size, the number of systems within scope, and whether the audit covers Type I or Type II. Many organizations also use a SOC 2 compliance automation platform to manage controls and documentation, which often ranges from $5,000 to $30,000 per year depending on features and expert support services.
Internal effort also contributes to total cost, as engineering, security, and operations teams allocate time to implement controls, maintain compliance documentation, and support audit reviews. Structured GRC platforms help reduce manual coordination and lower the operational burden across these teams.
Top 5 SOC 2 compliance platforms for SaaS in 2026
Many SaaS companies use SOC 2 platforms and compliance automation software to achieve and maintain continuous compliance. Here are 5 of the best compliance platforms used by SaaS companies to streamline SOC 2 compliance management:
1. Scytale
Scytale is the ultimate AI-powered compliance automation platform for SaaS companies, providing a clear path to SOC 2 readiness without adding operational strain. It seamlessly integrates with your cloud infrastructure and security tools to automatically gather evidence and continuously monitor controls, reducing manual work and boosting efficiency.
With AI-driven automation, multi-framework management, expert GRC support, and the unique AI GRC agent, Scy, Scytale allows SaaS teams of all sizes to manage SOC 2, ISO 27001, GDPR, HIPAA, SOX ITGC, and more in one central AI hub. Guided onboarding and expert compliance support enable you to achieve audit readiness faster, maintain SOC 2 compliance effortlessly, and simplify GRC processes.
(Screenshot from Scytale’s website)
2. Vanta
Vanta is a well-known compliance automation platform for SaaS companies. It helps organizations prepare for SOC 2 compliance by integrating with cloud infrastructure and automating tasks like evidence collection and control monitoring.
Limitations:
- Multi-framework programs can require additional configuration
- Costs can increase as features and integrations expand
(Screenshot from Vanta’s website)
3. Drata
Drata is a compliance automation solution that focuses on automating evidence collection and providing real-time monitoring for SOC 2 compliance. It offers integrations with various cloud services and developer tools to streamline compliance workflows and centralize security data.
Limitations:
- Setup may require dedicated internal resources
- Workflow customization can take additional effort
(Screenshot from Drata’s website)
4. Secureframe
Secureframe provides a structured approach to managing compliance programs through integrations, policy templates, and automated evidence collection. It is commonly used by SaaS companies beginning their SOC 2 compliance journey.
Limitations:
- Some processes may remain manual
- Custom environments may require additional configuration
(Screenshot from Secureframe’s website)
5. Sprinto
Sprinto focuses on helping cloud-hosted companies automate SOC 2 readiness through control monitoring and automated evidence collection. The platform integrates with cloud services and security tools to monitor compliance progress.
Limitations:
- Feature sets may be complex for smaller teams
- Continuous compliance management still requires internal ownership
(Screenshot from Sprinto’s website)
Best SOC 2 compliance platforms for 2026
| Platform | Ideal for | Key strengths |
| Scytale | SaaS companies scaling compliance programs | Automated evidence collection, continuous control monitoring, multi-framework cross-mapping, custom integrations, tailored expert guidance, AI GRC agent |
| Vanta | Early-stage SaaS teams | Simple automation and integrations |
| Drata | Engineering-focused teams | Developer integrations and automation |
| Secureframe | Early compliance programs | Structured policy templates |
| Sprinto | Cloud-native SaaS teams | Automated monitoring workflows |
What mistakes do SaaS companies make with SOC 2?
Many SaaS companies underestimate the operational effort required to implement and maintain SOC 2 controls. As a result, several common mistakes can slow down audits, create unnecessary complexity, or delay sales opportunities.
Waiting until a customer demands SOC 2
Some companies only begin the SOC 2 process after a customer requests it during procurement. This reactive approach often creates pressure on security and engineering teams to implement controls quickly.
Scoping the SOC 2 audit too broadly
Organizations sometimes include too many systems or processes in the initial audit scope. A well-defined scope focused on core infrastructure and production environments makes the audit more manageable.
Writing aspirational policies instead of practical ones
SOC 2 policies must reflect how security processes actually operate within the organization. Auditors expect documentation to match real workflows rather than idealized or theoretical procedures.
Skipping automation and relying on manual processes
Manual evidence collection and documentation management can quickly become time-consuming. Automation platforms help centralize controls and streamline evidence collection across systems.
Treating SOC 2 compliance as a one-time project
SOC 2 requires ongoing control monitoring and operational discipline. Organizations that treat it as a continuous program are better prepared for future audits and customer security reviews.
AI-native GRC for how teams work today.

How Scytale helps SaaS companies get SOC 2 compliant
Preparing for SOC 2 requires coordination across engineering, security, and leadership teams. Scytale helps SaaS organizations manage SOC 2 controls, documentation, and audit preparation within a centralized, AI-powered platform that integrates with common cloud infrastructure and security tools, streamlining evidence collection and providing 24/7 visibility into security and compliance posture.
With Scytale’s AI-powered compliance automation platform and expert GRC team, you can achieve seamless, automated, and continuous compliance while focusing on scaling your business. The platform supports multiple frameworks, enabling teams to manage overlapping controls efficiently and streamline SOC 2 audit preparation and compliance.
FAQs about SOC 2 compliance for SaaS
Do all SaaS companies need SOC 2?
Not every SaaS organization requires SOC 2 immediately. Organizations selling to midmarket or enterprise customers often receive SOC 2 requests during vendor security reviews. If your product handles sensitive customer data or targets regulated industries, buyers expect formal proof of security controls through a SOC 2 attestation report.
Can a startup get SOC 2 compliant?
Yes. SaaS startups frequently pursue SOC 2 attestation during their first sales cycles. A startup with defined security controls, documented policies, and clear ownership of security processes meets audit requirements. Many startups pursue a SOC 2 Type I audit first to establish a structured GRC foundation.
How often do you need to renew SOC 2?
SOC 2 reports reflect control performance over a defined period. Most SaaS companies complete a SOC 2 Type II audit every year to maintain current assurance for customers and key stakeholders. Annual reports demonstrate consistent control operation and provide buyers with updated validation of your security program.
Can you get SOC 2 without a compliance platform?
Yes, it’s possible to prepare for SOC 2 without specialized software, but it will be significantly more resource-intensive and time-consuming. To save time, reduce complexity, and ensure a smoother process, it’s highly beneficial to leverage a leading AI-powered compliance automation platform like Scytale from the start of your compliance journey. By doing so, you can streamline audit preparation and improve overall efficiency.
What’s the difference between SOC 2 and ISO 27001 for SaaS?
SOC 2 focuses on validating operational security controls through an attestation report. ISO 27001 focuses on establishing a formal information security management system (ISMS) with structured governance and risk management processes. SaaS companies often pursue SOC 2 for customer assurance in North America and ISO 27001 for global markets.