TL;DR: SOC 2 framework
- SOC 2 is a U.S. security framework designed to help businesses of all sizes protect sensitive data.
- The SOC 2 framework is crucial for SaaS companies to demonstrate their commitment to data security and privacy.
- SOC 2 compliance involves meeting the relevant Trust Services Criteria (TSC) to secure customer data.
- The SOC 2 audit process helps you evaluate your company’s adherence to these standards.
- AI-driven SOC 2 compliance automation platforms like Scytale streamline your entire compliance journey, saving time and ensuring your business stays audit-ready.
As your SaaS business grows, so does the responsibility of protecting customer data. SOC 2 helps ensure that your company is up to the task. Think of it as a roadmap to secure your organization’s data practices and build long-lasting customer trust.
Understanding what SOC 2 is and how your business can use it to your advantage can seem complex at first, but with the right approach, it becomes a powerful tool for increasing credibility and gaining a significant competitive advantage. Let’s explore why this framework is essential for securing customer data, strengthening trust, and positioning your business for long-term success in the highly-competitive SaaS landscape.
What is the SOC 2 framework?
Developed by the American Institute of Certified Public Accountants (AICPA), the SOC 2 framework provides a comprehensive set of guidelines to help organizations, from fast-growing startups to well-established enterprises, manage and secure sensitive customer data.
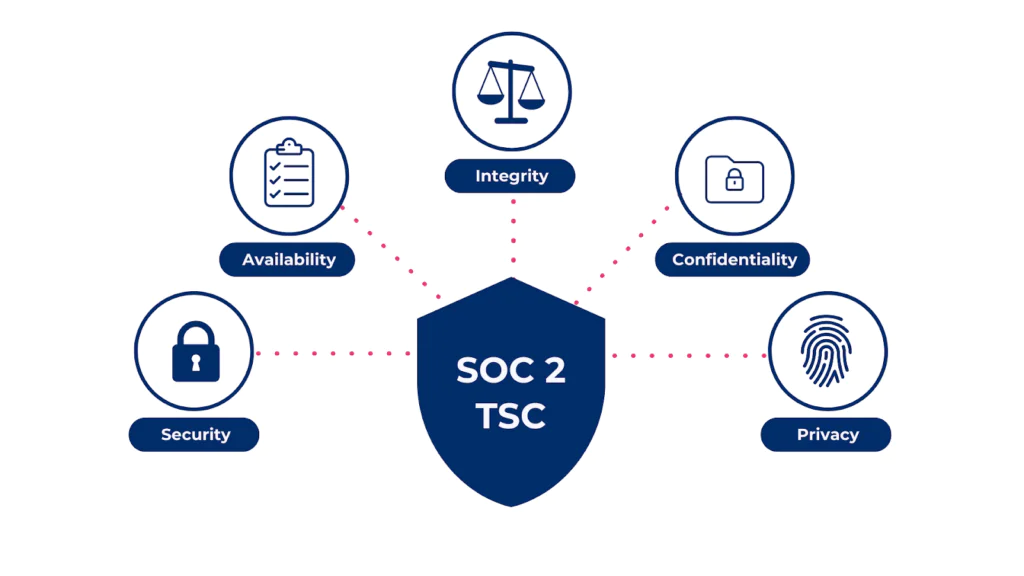
SOC 2 focuses on the five Trust Services Criteria (TSC): security, availability, processing integrity, confidentiality, and privacy, which we’ll dive into in more detail below. These criteria help businesses enhance their data protection practices, ensure the integrity of their systems, and maintain the privacy of sensitive information.
By following the SOC 2 framework, organizations can build a strong foundation for secure and reliable data management.
What are the 5 SOC 2 Trust Services Criteria?
One of the core components of the SOC 2 framework is the Trust Services Criteria (TSC), which consists of five key principles. These principles form the foundation of your SOC 2 audit and guide your organization’s approach to data security. It’s important to note that although only the relevant TSC apply, the Security principle is always mandatory.
SOC 2 framework: Trust Services Criteria
| Trust Services Criteria | Key focus area | Examples of practices or controls |
| 1. Security | Protecting data and systems from unauthorized access. | Firewalls, multi-factor authentication, intrusion detection. |
| 2. Availability | Ensuring services are accessible when needed. | Service monitoring, backups, disaster recovery. |
| 3. Processing integrity | Ensuring data is processed accurately and completely. | Data validation, transaction processing, systems monitoring. |
| 4. Confidentiality | Protecting sensitive data from unauthorized disclosure. | Data encryption, strict access control policies. |
| 5. Privacy | Protecting personal data and ensuring compliance with data privacy regulations. | Data collection and storage policies, GDPR and CCPA compliance. |
These five Trust Services Criteria form the backbone of your SOC 2 compliance and help ensure that your business handles data securely, reliably, and in compliance with industry standards. By adhering to these key principles, your company can demonstrate its commitment to maintaining the highest standards for data security, privacy, and operational efficiency.
💡 For more details on the Trust Services Criteria and how they apply to your business, have a look at our beginner’s guide to the five SOC 2 Trust Service Principles.
Who needs to comply with the SOC 2 framework?
The SOC 2 framework is widely adopted by SaaS providers, IT companies, and other organizations that handle sensitive customer data.
SOC 2 is a critical component of your Governance, Risk, and Compliance (GRC) strategy, helping to build trust with customers and stakeholders, especially in industries where data privacy protection is essential. Achieving and maintaining SOC 2 compliance demonstrates a company’s genuine commitment to handling sensitive information securely and responsibly.
Although primarily used in the U.S., SOC 2 is recognized globally as a highly respected standard for data protection and privacy.
Why the SOC 2 framework is crucial for SaaS organizations in 2026
For startups and scaling businesses dealing with sensitive data, SOC 2 compliance is a key driver of sustainable growth and security. Here’s why it’s essential for your business’s long-term success:
Building trust
SOC 2 compliance demonstrates to your customers that their data is in safe hands, fostering confidence in your business. Your SOC 2 report not only underscores your commitment to data protection but also strengthens your reputation in the market. It reassures customers and key stakeholders that security is a top priority, positioning your company as a reliable and trustworthy partner.
Gaining a competitive advantage
Many enterprises require SOC 2 compliance before engaging, making it crucial for securing contracts and partnerships. Achieving and maintaining SOC 2 boosts your credibility, attracting larger clients who prioritize security, and opening doors to new business opportunities.
Strengthening your risk management strategy
Adopting SOC 2’s Trust Services Criteria helps identify and mitigate security risks, requiring businesses to implement strong SOC 2 controls to prevent security incidents such as data breaches. Adhering to SOC 2 compliance requirements reduces risks, enhances security, and protects against costly breaches and reputational damage.
Improving operational efficiency
The SOC 2 audit process helps improve internal controls, making your business more efficient and secure. It leads to better practices in data access, security awareness training, and workflows.
By automating the SOC 2 audit preparation and compliance process, your business can streamline operations, boosting security and efficiency while ensuring your business stays audit-ready around the clock.
What are the benefits of following the SOC 2 framework?
Adopting this SOC framework provides significant benefits for your SaaS organization. By aligning with SOC 2 compliance requirements, you not only enhance your overall security posture but also showcase a strong commitment to data protection best practices.
Here are the key benefits to consider:
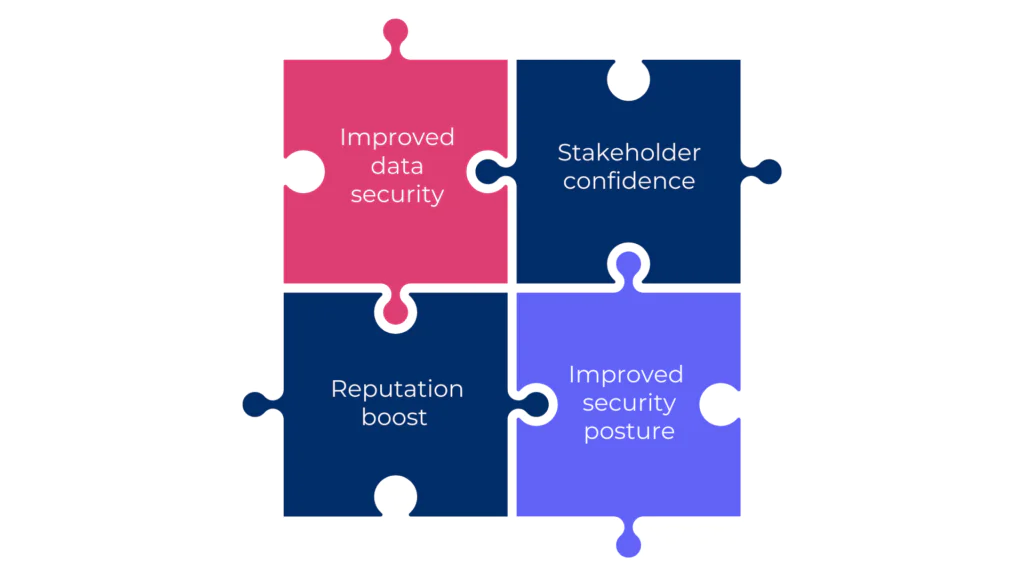
1. Improved data security
Following SOC 2 ensures the implementation of strong security controls to protect data from unauthorized access and security threats. These controls include access management, encryption, and regular monitoring to prevent data breaches. By securing your data, you reduce the risk of cyber-attacks and protect customer data.
2. Stakeholder confidence
Successfully completing a SOC 2 audit and receiving your SOC 2 report sends a powerful message to customers and stakeholders that their data is secure and meets industry standards. By showcasing your dedication to best-in-class security practices, you not only build stronger business relationships but also boost customer loyalty and retention.
3. Reputation boost
Achieving SOC 2 compliance enhances your company’s reputation by showcasing your dedication to data security and privacy. It positions you as a trustworthy partner, attracting clients who prioritize strong security practices and solidifying your standing in the marketplace.
4. Improved security posture
SOC 2 provides a structured framework for improving data security and privacy, strengthening your overall security posture. Applying SOC 2 practices also encourages a security-conscious culture, where employees better understand their role in keeping the organization compliant.
By leveraging the best SOC 2 compliance software like Scytale, your organization can reap the rewards and achieve continuous SOC 2 compliance with minimal effort and maximum efficiency.
How to achieve and maintain compliance with the SOC 2 framework
The SOC 2 framework is designed to be straightforward and manageable. The key to success lies in identifying your organization’s specific risks, implementing the necessary controls, and continuously monitoring your security posture.
With the right SOC 2 tools and strategy, your business can efficiently meet compliance goals and maintain compliance with SOC 2 as well as other critical security and privacy frameworks.
Let’s walk through the key steps to help you on your journey to SOC 2 compliance:
Step 1: Define scope and assess security risks
Start by defining the scope of your SOC 2 audit, including the relevant Trust Services Criteria and the systems, data, and processes in scope. From there, conduct a thorough security risk assessment to identify vulnerabilities in areas such as data access, storage, and processing, helping you focus your efforts on protecting sensitive information.
Step 2: Design and implement SOC 2 controls
Once risks have been identified, implement the necessary internal controls to mitigate those risks. This could involve setting up strong firewalls, encryption protocols, or ensuring proper access management for employees. By putting these controls in place, you create a secure environment for your data and systems.
Step 3: Select a SOC 2 auditor
A SOC 2 audit must be conducted by an independent, licensed CPA firm with expertise in IT audits and SOC 2 requirements. The auditor should follow AICPA guidelines and be familiar with your industry and company size. Audit timelines and costs will vary depending on the firm you choose.
Step 4: Conduct a SOC 2 readiness assessment
Before the formal audit, a readiness assessment helps determine whether your organization is prepared. This typically includes a gap analysis to evaluate whether your current security controls align with SOC 2 requirements and to identify areas that need remediation.
Step 5: Complete the SOC 2 audit
Once the readiness assessment is complete, it’s time for the official SOC 2 audit. The auditor reviews evidence to confirm that the controls are designed and operating as described by management and in line with SOC 2 criteria. The monitoring period will depend on whether a SOC 2 Type I or Type II report is being pursued.
Step 6: Review and understand the SOC 2 report
A SOC 2 report is an attestation, not a pass or fail outcome. It reflects the auditor’s opinion on whether your controls meet the Trust Services Criteria and highlights any exceptions. If everything aligns, the auditor will issue the SOC 2 report, confirming your compliance and giving you the green light to move forward with confidence!
Step 7: Monitor controls and repeat annually
SOC 2 reports are valid for 12 months and must be renewed annually. Continuous monitoring of controls throughout the year, along with regular updates to policies and procedures, helps maintain compliance and simplifies audit prep going forward.
🎙️Tune in to this podcast episode as Charissa Kim offers a fresh, Gen Z perspective on making SOC 2 more engaging and relatable: A gen Z’s take on making SOC 2 suck less.
Get SOC 2 Compliant 90% Faster
How Scytale simplifies SOC 2 framework management
SOC 2 compliance can feel overwhelming, especially with all the other demands on your time. But it doesn’t have to be.
Scytale streamlines your SOC 2 journey from start to finish by automating critical tasks like evidence collection, continuous monitoring, risk management, and audit readiness. Our AI-powered platform, backed by expert GRC guidance and Scy, our next-gen AI agent, ensures you stay on track with every SOC 2 requirement.
With Scytale, SOC 2 compliance is quick, effortless, and seamlessly woven into your daily operations, allowing you to focus on scaling your business while we handle the compliance heavy lifting.
FAQs about SOC 2 compliance
Is SOC 2 a cybersecurity framework?
Yes, SOC 2 is considered a cybersecurity framework, though it goes beyond just security. It focuses on five key principles: security, availability, processing integrity, confidentiality, and privacy. These principles ensure that a company’s data is protected, its systems are accessible, and its processes are reliable, making SOC 2 a comprehensive framework for safeguarding data and a key component of any SaaS business’s approach to security and compliance.
How does SOC 2 differ from other cybersecurity frameworks in practice?
SOC 2 is specifically tailored for service providers, especially SaaS companies handling sensitive customer data. While it shares similarities with other cybersecurity frameworks, SOC 2 uniquely focuses on the Trust Services Criteria. These criteria address the security of data, the reliability and accessibility of systems, and the protection of privacy. What sets SOC 2 apart is its emphasis on audit and reporting practices rather than prescriptive technical standards, making it particularly valuable for service-oriented businesses that need to demonstrate their commitment to data protection and continuous compliance.
What are the 5 principles of SOC 2?
The five principles of SOC 2 are security, availability, processing integrity, confidentiality, and privacy. To achieve SOC 2 attestation, businesses must meet the requirements of the relevant principles; however, the Security principle is always mandatory. The best SOC 2 compliance software, like Scytale, streamlines this process by automating critical tasks like continuous control monitoring and providing expert guidance, helping companies achieve and maintain compliance with ease
What is the SOC 2 Type 2 framework?
SOC 2 Type 2 evaluates the effectiveness of a company’s controls over a period, usually 6 to 12 months, offering a deeper, continuous assessment compared to Type 1, which only reviews controls at a specific point in time. A SOC 2 Type 2 report provides insights into the consistency and effectiveness of security and privacy measures over time. The best SOC 2 automation platforms like Scytale help companies maintain continuous SOC 2 compliance, ensuring adherence to SOC 2 Type 2 requirements.